Podcast: Play in new window | Download
Subscribe: Apple Podcasts | Android | Email | Google Podcasts | Stitcher | TuneIn | Spotify | RSS
On this episode of The Vonu Podcast, I welcome back friend & hardware hacker, Jamin Biconik, to get an update on The GhostSystem, a practical model for both digital and physical self-sovereignty.
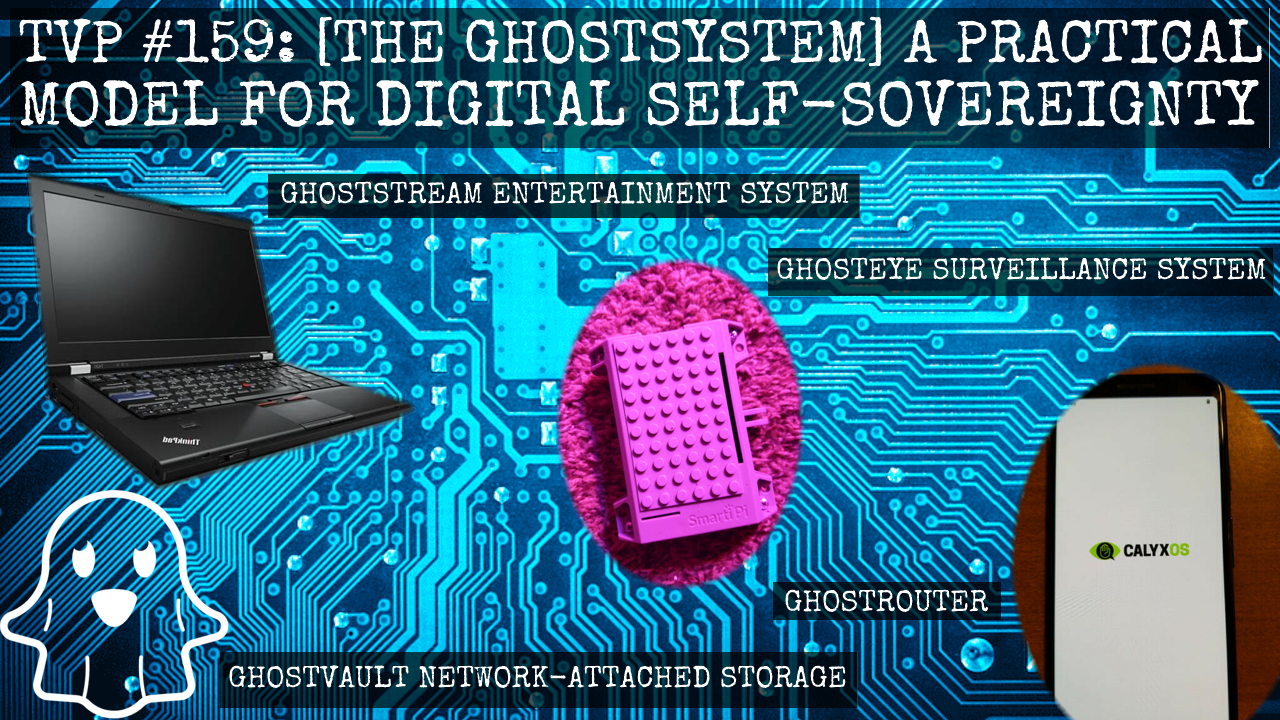
The GhostSystem features:
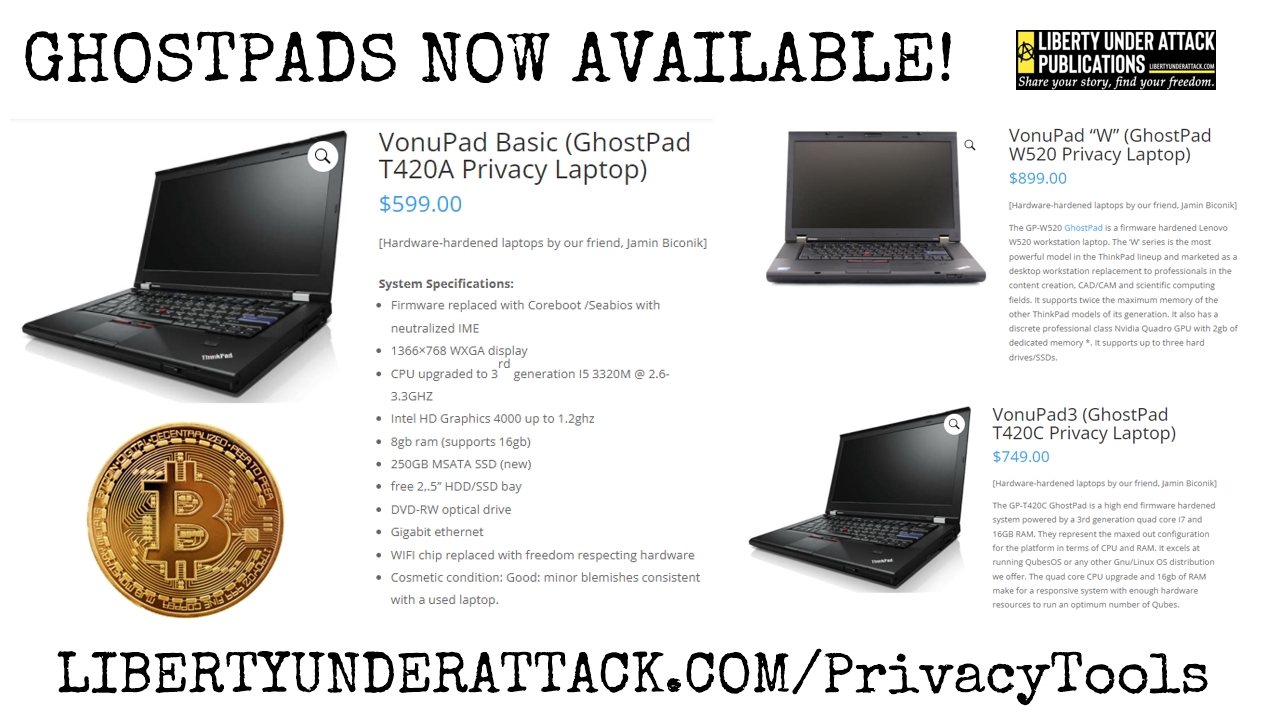
- GhostPad for research, communications, and the most private personal data like a private journal.
- GhostPhone for maximum mobile autonomy
- GhostBox FreedomBox for self hosted services like secure messaging, private search engine and advanced network wide ad and tracker filtering
- GhostStation for gaming, and content creation
- GhostBox Sentinal network security system with PiAlert and PI-Hole
- GhostRouter to secure your network from outside threats
- GhostVault NAS to store and serve media
- GhostStream Entertainment system as a smart TV replacement
- GhostEye surveillance and security system
And while Jamin will offer all of these (and we’ll offer special bundles on the LUA Publications website), you can also use this model & the knowledge found herein to build out all your own infrastructure.
SHOW GUIDE:
- Jamin and I provide some homesteading updates, the good & the bad
- The utility of sunchokes/Jerusalem artichokes; great famine food, escape crop, and Edgar Cayce’s discovery of their use in so-called “type 1 diabetes” (inulin & insulin content, allegedly)
- The setup for the GhostSystem: Speaking in terms of the Second Realm, just as we’re rebuilding every institution upon these frameworks of peace and truth, the GhostSystem will do for each need/use case
- Jamin provides an update on the FreedomBoxes & the coming new P.A.Z.NIA Committee of Correspondence
- Jamin: the main problem is that most folks don’t understand their own threat model; these tools aren’t “choices” anymore, if one wants to remain free
- The problem of geo-fencing: being targeted by location data/metadata
- Jamin starts to run through the GhostSystem, starting with a GhostPad update & his newest iteration, the GhostSystem, for content creation & gaming
- The core tenets of a GhostSystem: the device is not able to be out-of-band managed (exception being the GhostPhone, no way around it if you connect to a mobile network)
- The GhostSystem (and privacy-enhancing tools like it) empowers users over their products, and not the products over their users
- The GhostRouter and GhostBox Sentinel are root solutions to solve a lot of potential problems — i.e., if you own someone’s router, you own someone’s Internet connection (and the industry standard is vulnerability)
- The GhostSystem is a system of compartmentalizing your digital life, much like a self-liberator/vonuan take steps to compartmentalize aspects of their life from the servile society
- Titillating conversation about chip/board shortages
- The GhostBox Sentinel, the advantages of PiAlert and PiHole, and Encrypted DNS as a replacement for the need of a third-party VPN
- Targeting someone for advertising is the just a different algorithm than targeting someone for harassment
- It’s getting to the point that free-and-open source software/hardware is becoming easier than proprietary providers, merely because they lock you down so much and add in so many inconveniences/vulnerabilities
- A great place to start: The (Coming) Crypto-Vonuan Bundle (A GhostPad, GhostPhone, & A Faraday Bag for the Phone)
- Every element of the GhostSystem is currently available, special bundles forthcoming via the Liberty Under Attack Publications website
- Also coming: a GhostSystem Guide/Book via LUA Publications
~~~
HEALTH LIBERATION/SELF-LIBERATION SPECIAL OFFER:
Interested in your own AquaCure? Save $125 with coupon code “vonu“, and help support the P.A.Z.NIA Department of Health/Wellness at the same time!

~~~
[DOWNLOAD FOR FREE!]



2 Replies to “TVP 159: [The GhostSystem] A Practical Model for Digital Self-Sovereignty with Jamin Biconik”